Key Programs
- Key Programs
- Information Security and Certification Audits
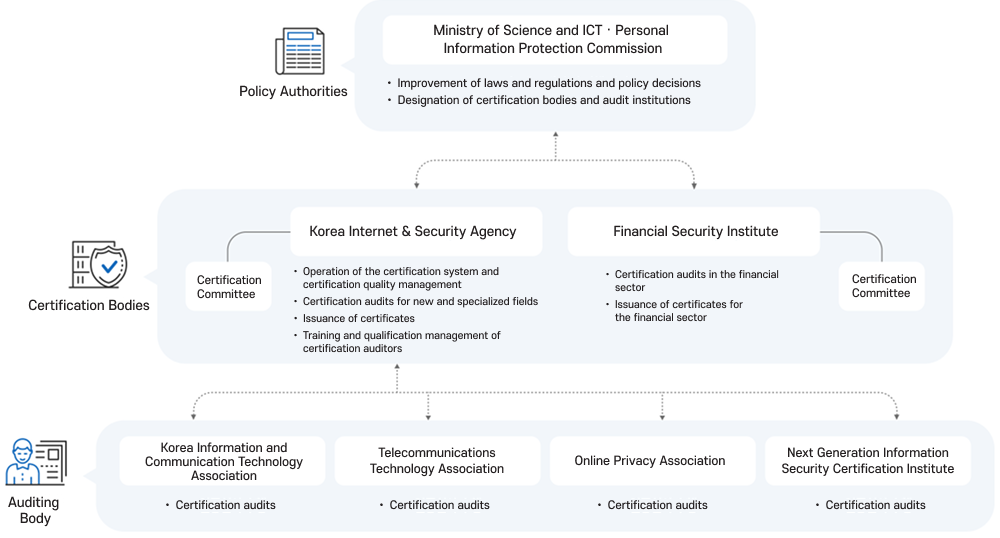
About the Personal Information & Information Security Management System Certification
A certification system that evaluates and certifies whether an organization has systematically established, implemented, inspected, and improved administrative, technical, and physical safeguards to protect information assets and personal information.

Program Objective
To enhance the level of information security within organizations and strengthen personal information protection activities through certification of information security and personal information protection management systems.
Legal Basis
- Article 47 of the Act on Promotion of Information and Communications Network Utilization and Information Protection
- * Enforcement Decree Articles 47–54, Enforcement Rule Article 3, Article 32-2 of the Personal Information Protection Act
- Enforcement Decree Articles 34-2–34-8
- Notification on Certification of Information Security and Personal Information Protection Management Systems
Operational Basis
- In accordance with Article 47(6) and (7) of the Act on Promotion of Information and Communications Network Utilization and Information Protection and Article 53-2 of its Enforcement Decree, and Article 32-2(5) of the Personal Information Protection Act and Article 34-6 of its Enforcement Decree, the Korea Information and Communication Technology Association has been designated as an information security and personal information protection management system audit institution (ISMS-P-SIM-02).
인증유형
- Information Security and Personal Information Protection Management System Certification (ISMS-P)
- Information Security Management System Certification (ISMS)
- Information Security Management System Preliminary Certification
Certification Types
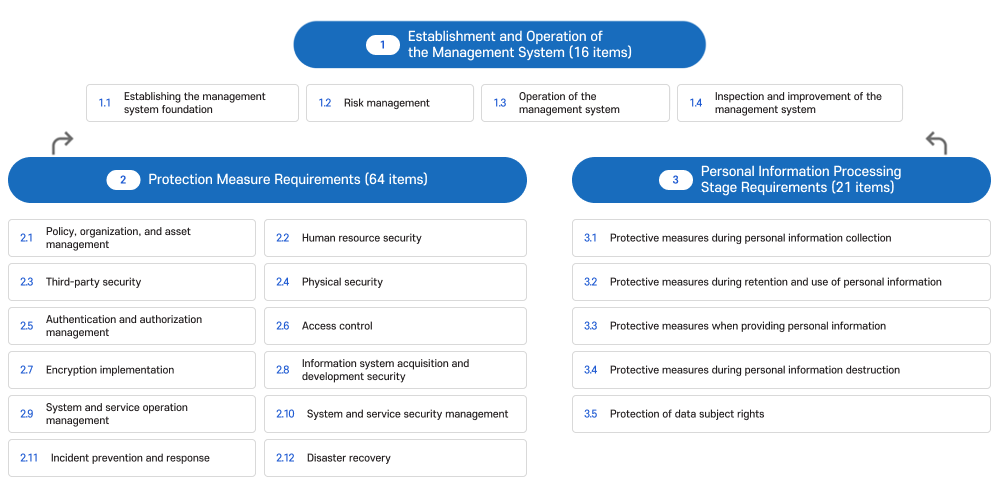
Certification Criteria
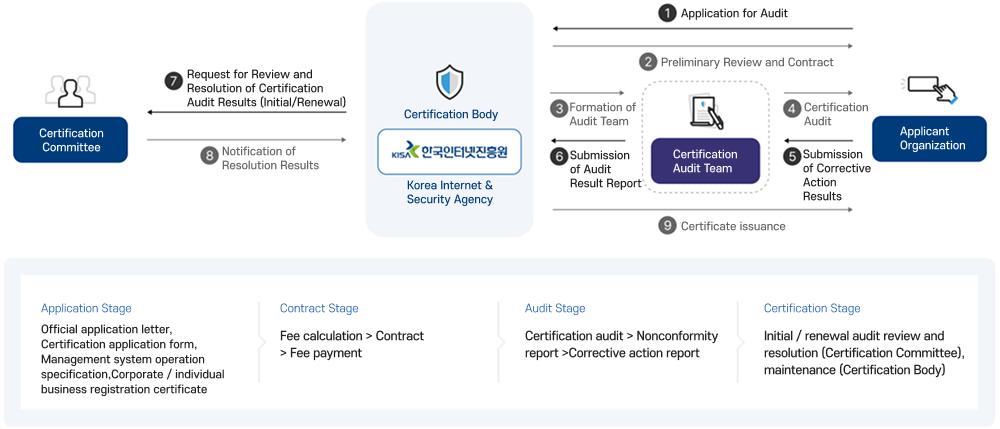
Certification Audit Procedure
Types of Certification Audits
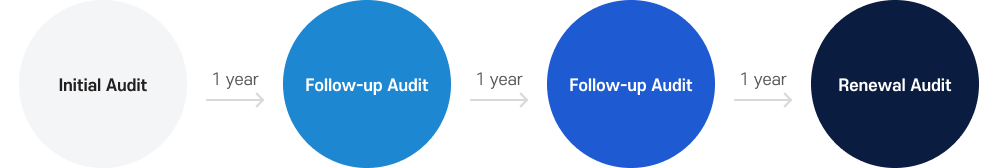
| Category | Description |
|---|---|
|
Initial Audit |
An audit conducted when obtaining certification for the first time. It is also conducted when certification is reapplied for due to significant changes in the certification scope. Upon successful completion, a 3-year validity period is granted. |
|
Follow-up Audit |
An audit conducted at least once every year during the certification validity period to verify that the information security management system continues to be properly maintained. Conducting this audit annually is required to maintain the granted 3-year validity period. |
|
Renewal Audit |
An audit conducted to extend the validity period of the information security management system certification. |
Certification Audit Eligible Applicants
| Category | Criteria and Legal Basis for Mandatory Applicants |
|---|---|
|
Mandatory Applicants |
• Information and Communications Network Service Providers (ISP) Entities licensed under Article 6(1) of the Telecommunications Business Act that provide information and communications network services in Seoul and all metropolitan cities |
|
• Internet Data Center Operators (IDC) Operators of integrated information and communications facilities under Article 46 of the Act on Promotion of Information and Communications Network Utilization and Information Protection |
|
|
• Advanced general hospitals with annual revenue or income of KRW 150 billion or more, and universities with more than 10,000 enrolled students Advanced general hospitals under Article 3-4 of the Medical Service Act Schools under Article 2 of the Higher Education Act |
|
|
• Entities with annual revenue of KRW 10 billion or more in the information and communications service sector (previous fiscal year for corporations) |
|
|
• Entities with more than 1 million average daily users in the previous year |
|
|
Voluntary Applicants |
• Organizations not subject to mandatory certification but wishing to obtain certification voluntarily |
|
Preliminary Certification |
• Certification conducted prior to full certification to assess readiness for an information security management system |
|
Certification Exceptions |
• Small enterprises under Article 2(2) of the Framework Act on Small and Medium Enterprises |
|
• Medium-sized enterprises with less than KRW 30 billion in revenue in the information and communications service sector |
|
|
• Medium-sized enterprises with KRW 30 billion or more in revenue in the information and communications service sector but without major ICT infrastructure (e.g., proprietary servers, network equipment, security solutions) used for providing their own services |